Businesses today are facing a ransomware threat that is more aggressive and damaging than anything seen before. Every week, organizations discover their systems locked, their data stolen, and their reputations on the […]


Businesses today are facing a ransomware threat that is more aggressive and damaging than anything seen before. Every week, organizations discover their systems locked, their data stolen, and their reputations on the […]

Online dating has changed the game, sure. But let’s not kid ourselves, the internet is full of predators. You swipe, you match, you think you’ve found “the one,” and BOOM, you’re in […]

Remote work has been a game-changer. Lower overhead. Happier employees. Wider talent pool. All wins. But there’s a catch: every remote login, home Wi-Fi network, and personal device your team uses is […]

Not every cyber risk comes from the outside. Some walk right in the front door … in the form of tools, apps, and devices your own employees are using without asking. It’s […]
Most cyberattacks don’t start with a mastermind hacker running lines of code in some movie-style lair. They start with something small. A sticky note with a password written on it.A rushed click […]
Business leaders today are spending far less time behind a desk and far more time working on the go. Whether it’s meetings, travel, remote work, or simply managing a busy day, the […]

Cybersecurity threats don’t stand still. They adapt. They get smarter. And every time technology takes a step forward, attackers figure out how to twist it to their advantage. The three threats below […]
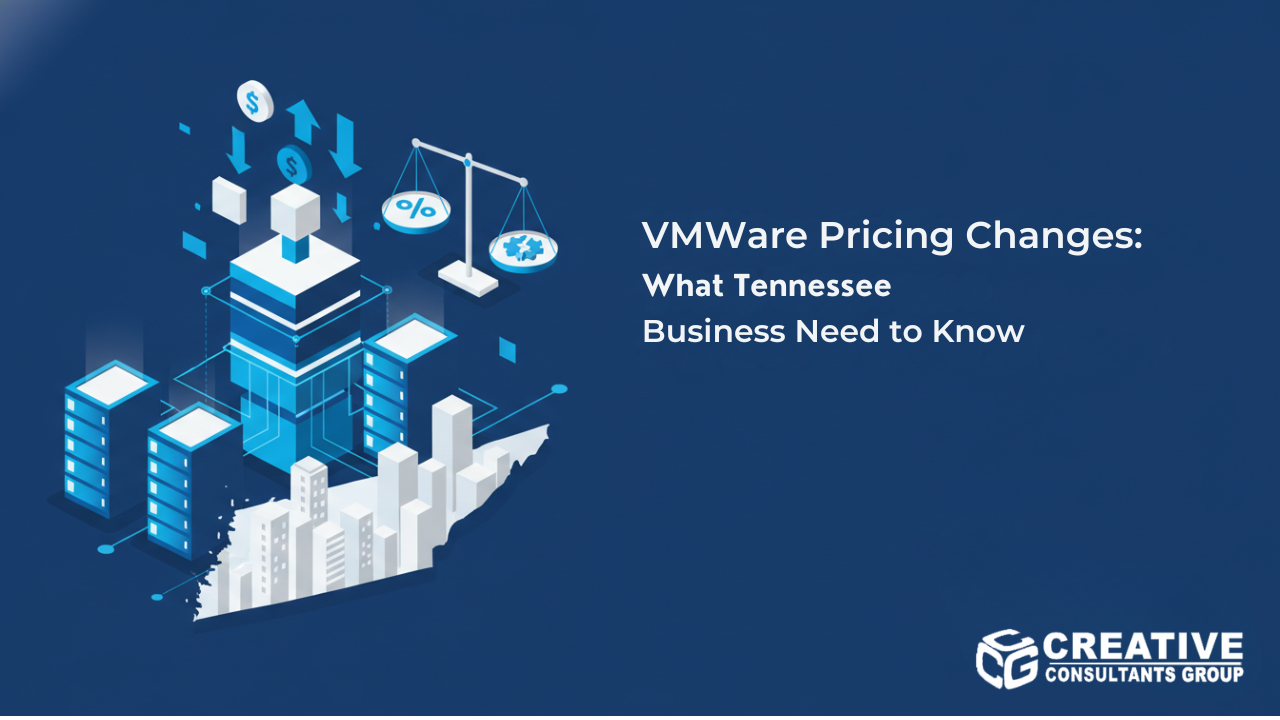
VMware customers are facing one of the most significant shifts in virtualization strategy in recent years. Following Broadcom’s acquisition of VMware, Tennessee businesses are seeing major changes to pricing, licensing, and product […]
Remote work isn’t going away … and neither are the risks that come with it. Every time someone logs in from a coffee shop, a hotel lobby, or their personal laptop at […]
Cybercriminals don’t take days off … and they don’t wait for a “good” time to strike. They prey on moments when people are busy, distracted, or rushing. The tactics change, but the […]

Hackers don’t always kick in the digital door. Sometimes, they just talk you into opening it. This is social engineering; hacking people instead of systems. It works because humans are wired to […]

Cyber disasters don’t start with genius hackers in hoodies.They usually start with something simple. A missed update. A gullible click. A tiny configuration mistake no one double-checked. Then they explode … taking […]